Protect Your Database in a Distributed World with IP Access List

Security and governance are top priorities for enterprises that adopt cloud-first initiatives. DataStax Astra DB, the multi-cloud database-as-a-service (DBaaS) built on Apache Cassandra™, can be a perfect complement to your cloud strategy: it’s cloud native, autoscales, and lowers your total cost of ownership (TCO). DBaaS offerings are held to a higher standard than many other cloud services because they manage an enterprise’s most precious asset: data.
Role-based access management restricts access by user or client application, but many enterprises need a stronger security posture. They need to restrict network access to safe IP addresses—especially in the new world of remote and distributed work. IP Access List is indicative of our continuous innovation in Astra DB, building upon security features such as end-to-end encryption including encryption on the wire with mTLS , VPC peering, SOC 2 compliance, and more.
Astra DB’s IP Access List addresses these concerns by enabling users to custom configure IPs and CIDR blocks that can access Astra DB hosted resources, including REST, GraphQL, Swagger, and CQLsh. This lets enterprises restrict access from select office and home networks. Optionally, if using peered networks, public endpoints can be turned off to remove access over the public internet. IP Access List, when combined with other Astra DB features such as Role-Based Access Control (RBAC) and your organization’s internal controls, enable a robust security practice.
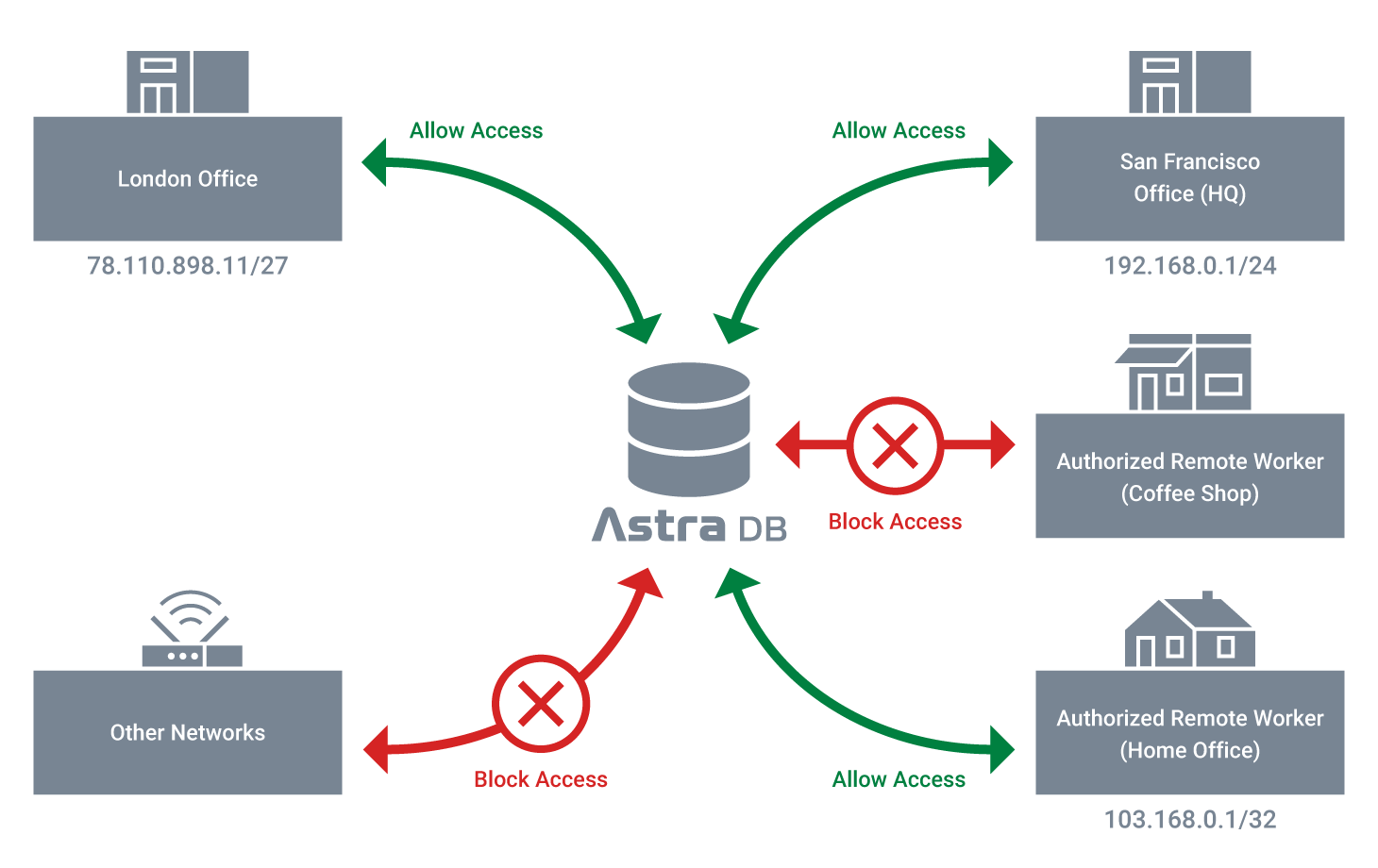
This addresses two popular use cases:
- Enterprises can set up access such that all database operations can be performed by the user only when on the secure corporate network; if the user attempts access from outside the perimeter, all access is blocked for the user.
- IP Access List also addresses use cases where access to data must be restricted to certain countries to adhere to compliance regulations.
This feature also addresses use cases that require the ability to turn off all public access when using network peering
Getting started with IP Access List
To restrict access, start by logging in to astra.datastax.com.
- From the dashboard, select the database that you want to restrict access to and navigate to the settings page to configure your IP Access List
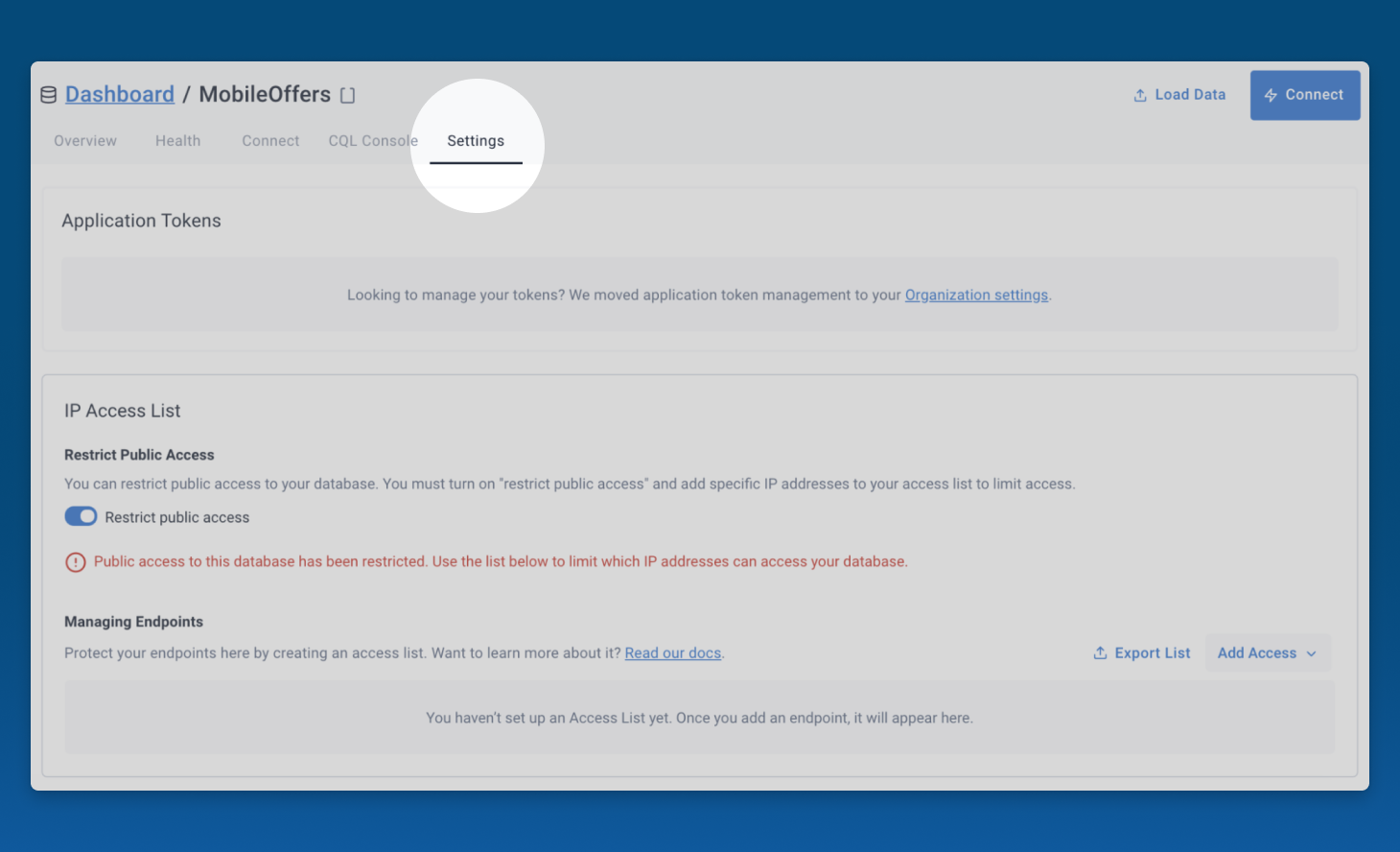
By default all endpoints are open to public access.
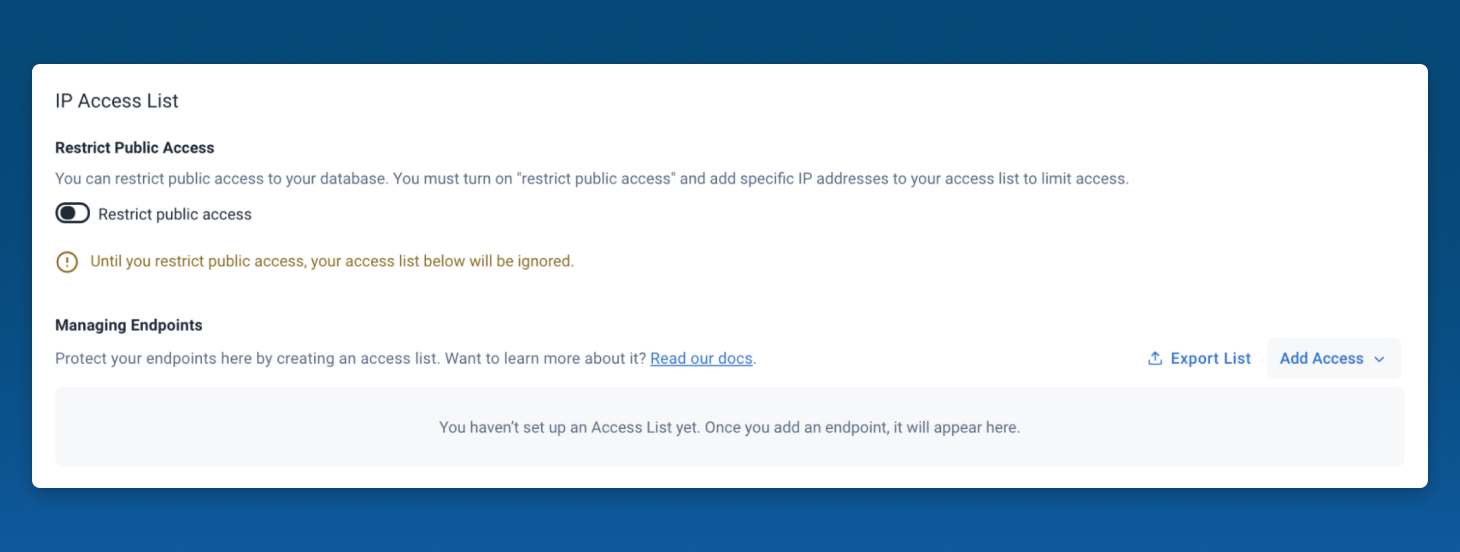
Access can restricted using one of the below options:
Turn off public access entirely:
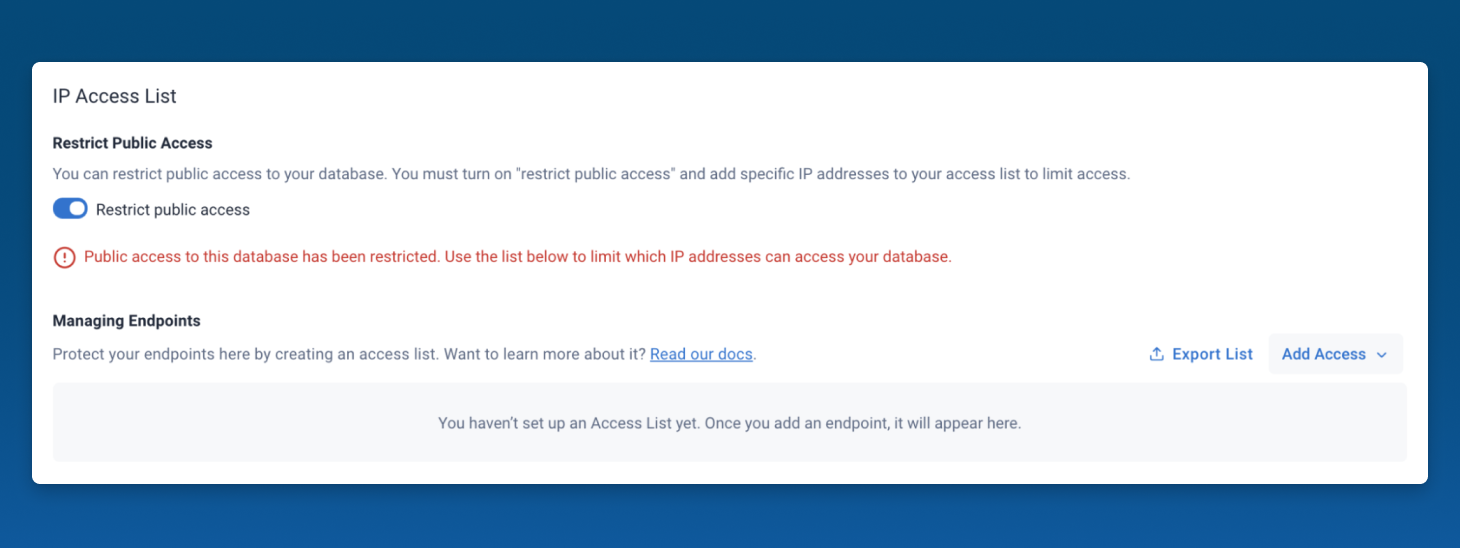
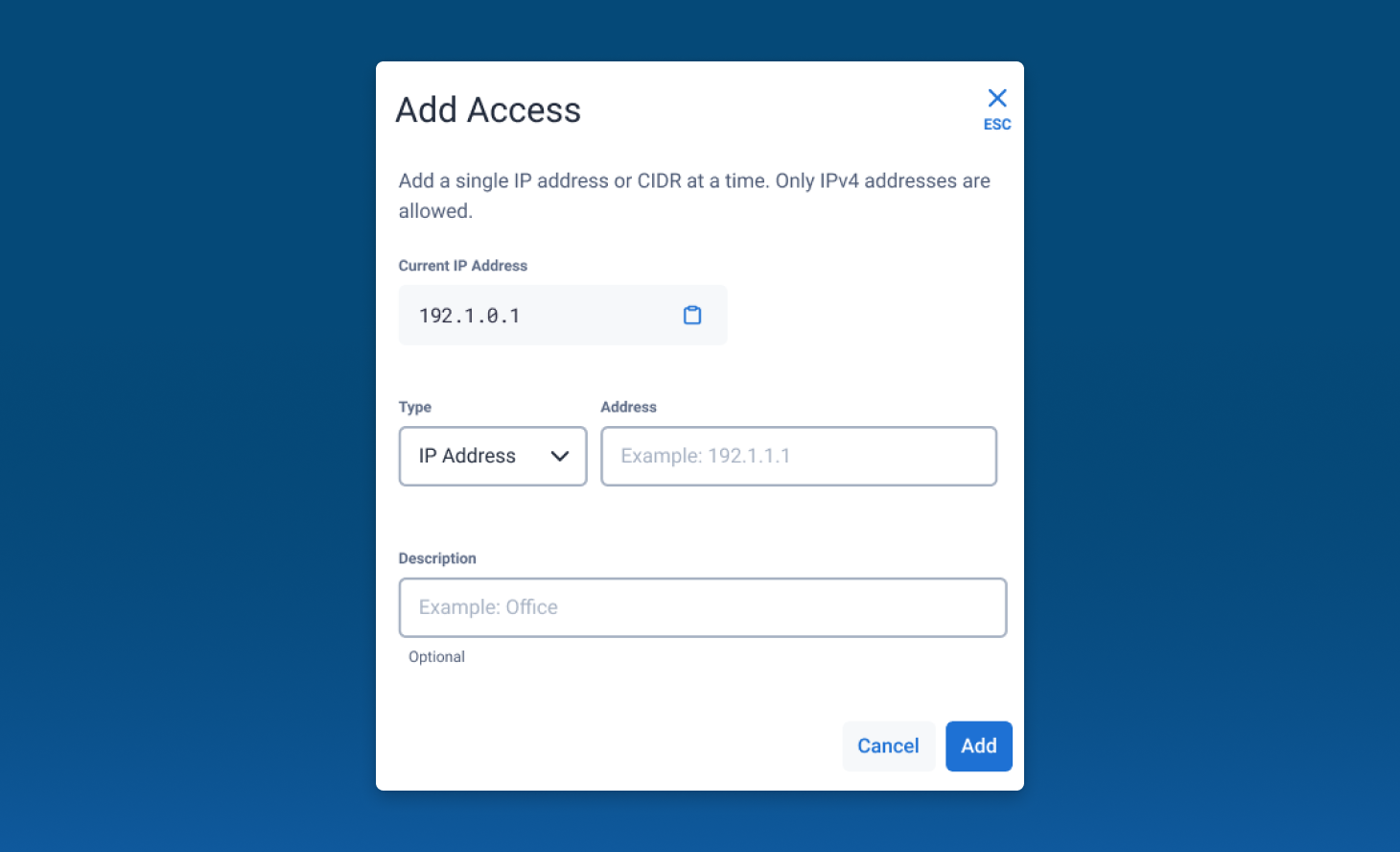
Selectively allow IP/CIDR for access:
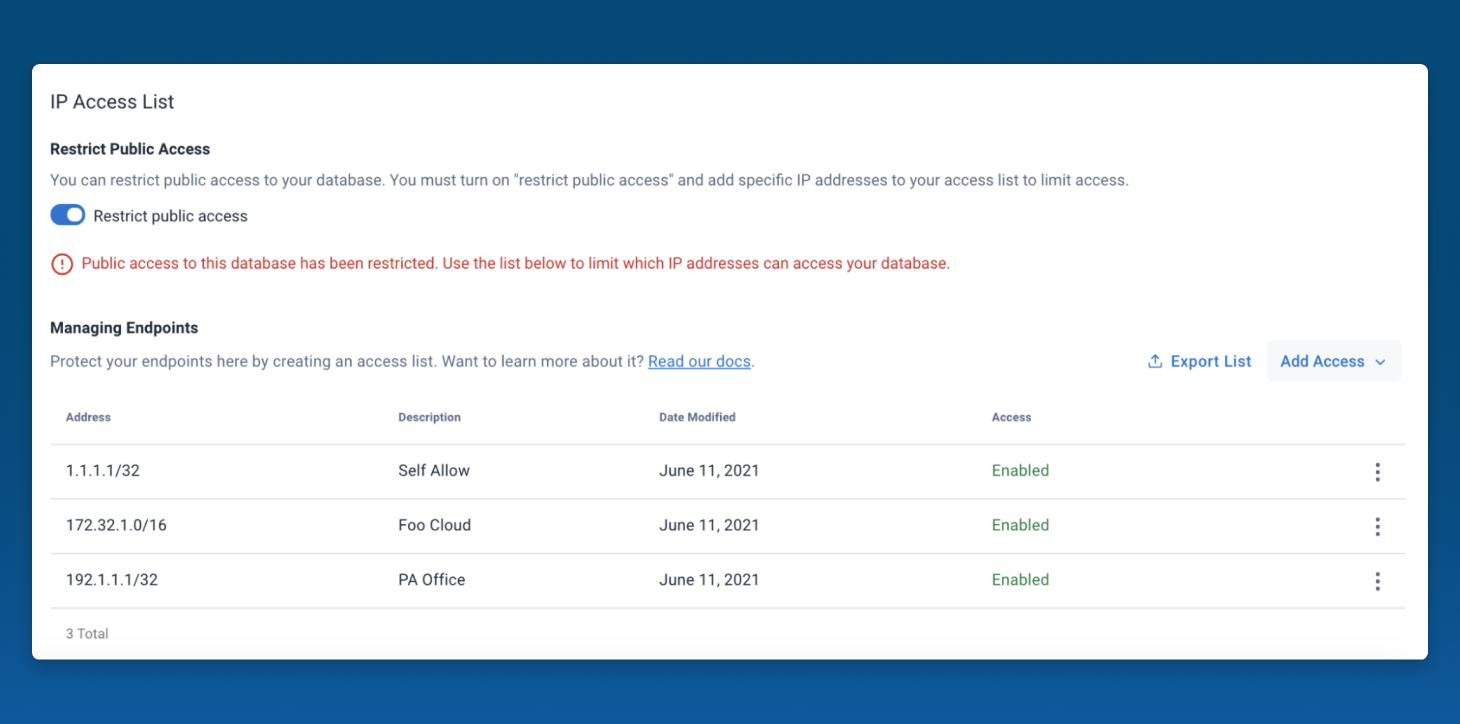
Once an IP or a CIDR block is added to the table and the toggle is set to “Restrict public access,” all other IPs are blocked. After that step is completed, the below endpoints are restricted for access:
- CQL
- REST
- GraphQL playground
- Swagger
- CQLsh
In addition to the Astra DB UI workflow, IP Access List can be configured using the Astra DevOps API.
For more detailed information on IP Access List, please review the Astra DB documentation.
Astra DB is the fastest and easiest way to spin up secure Cassandra clusters. If you’re not using Astra DB, get started without a credit card by registering for an account at https://astra.datastax.com/register and use your Google or GitHub account to sign in (you can also sign up using your email address). For feedback and comments, reach out to astra-pm@datastax.com.




